AI Companions: Best Free Apps, Advanced Chat, and Safety Tips for 2026
Here’s the straightforward guide to this year’s « AI companions » landscape: what’s actually complimentary, the way realistic communication has progressed, and methods to remain safe while navigating AI-powered deepnude apps, web nude synthesis tools, and NSFW AI tools. One will get an insightful pragmatic examination at the industry, quality metrics, and a safety-oriented safety framework you can implement immediately.
The phrase « AI companions » includes three different product types that often get mixed up: AI-powered chat companions that emulate a girlfriend persona, mature image creators that synthesize bodies, and AI undress applications that try clothing elimination on real photos. Every category carries different pricing models, realism ceilings, and danger profiles, and confusing them together is when most users get burned.
Understanding « AI virtual partners » in 2026
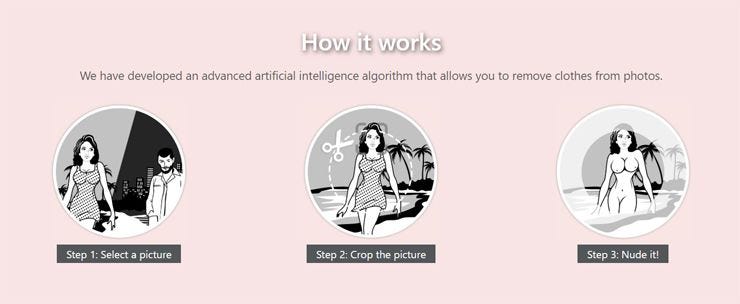
AI girls presently fall into several clear buckets: chat chat applications, mature image generators, and apparel removal tools. Relationship chat concentrates on character, recall, and audio; image synthesizers aim for realistic nude synthesis; undress applications attempt to deduce bodies beneath clothes.
Companion chat platforms are the least legally dangerous because they create virtual personalities and fictional, synthetic media, often protected by NSFW policies and user rules. NSFW image synthesizers can be less risky if utilized with completely synthetic inputs or virtual personas, but they still create platform policy and privacy handling issues. Deepnude or « clothing removal »-style tools are most riskiest type because they can be misused for non-consensual deepfake content, and numerous jurisdictions now treat that like a prosecutable offense. Framing your goal clearly—relationship chat, generated fantasy content, or authenticity tests—establishes which route is correct and how much much safety friction you must accept.
Market map and key players
The market splits by function and by methods through which the outputs are generated. Services like these tools, DrawNudes, various platforms, AINudez, Nudiva, and related services are advertised as automated nude generators, internet nude generators, or intelligent undress applications; their selling points usually to revolve around quality, performance, price per render, and security promises. Companion chat platforms, by difference, focus on dialogue depth, n8ked login response time, recall, and voice quality rather than concerning visual results.
Because adult automated tools are volatile, judge vendors by their policies, not their advertisements. At minimum, look for a clear explicit permission policy that forbids non-consensual or underage content, a clear data storage statement, a way to erase uploads and outputs, and open pricing for tokens, subscriptions, or interface use. If any undress app emphasizes marking removal, « without logs, » or « capable of bypass security filters, » treat that like a red flag: ethical providers won’t encourage harmful misuse or rule evasion. Without exception verify built-in safety controls before you share anything that could identify a genuine person.
Which AI girl apps are actually free?
Many « free » alternatives are freemium: users will get a limited amount of creations or messages, ads, branding, or restricted speed unless you pay. A truly zero-cost experience typically means reduced resolution, processing delays, or extensive guardrails.
Anticipate companion chat apps to offer a modest daily allotment of communications or points, with adult content toggles often locked behind paid subscriptions. NSFW image creators typically include a handful of basic credits; upgraded tiers unlock higher resolutions, quicker queues, personal galleries, and personalized model configurations. Undress apps infrequently stay free for long because GPU costs are substantial; they often move to individual usage credits. When you desire zero-cost experimentation, consider on-device, open-source systems for communication and SFW image evaluation, but avoid sideloaded « clothing removal » binaries from questionable sources—these represent a typical malware delivery method.
Comparison table: selecting the appropriate category
Pick your application class by matching your objective with potential risk one is willing to assume and any required consent you can get. The table below outlines what features you typically get, what expenses it costs, and how the pitfalls are.
| Classification | Typical pricing model | Features the no-cost tier offers | Main risks | Optimal for | Consent feasibility | Privacy exposure |
|---|---|---|---|---|---|---|
| Chat chat (« Digital girlfriend ») | Freemium messages; subscription subs; additional voice | Finite daily interactions; basic voice; NSFW often locked | Revealing personal details; parasocial dependency | Role roleplay, companion simulation | Strong (virtual personas, zero real persons) | Medium (conversation logs; review retention) |
| NSFW image generators | Tokens for renders; premium tiers for HD/private | Low-res trial tokens; branding; queue limits | Rule violations; leaked galleries if without private | Generated NSFW art, stylized bodies | Good if fully synthetic; get explicit authorization if employing references | Significant (files, descriptions, generations stored) |
| Nude generation / « Garment Removal Application » | Per-render credits; scarce legit free tiers | Occasional single-use attempts; prominent watermarks | Non-consensual deepfake responsibility; malware in shady apps | Scientific curiosity in supervised, permitted tests | Minimal unless each subjects specifically consent and are verified persons | Significant (face images submitted; critical privacy risks) |
To what extent realistic is chat with virtual girls currently?
State-of-the-art companion communication is unusually convincing when developers combine strong LLMs, temporary memory systems, and character grounding with natural TTS and low latency. Any inherent weakness shows under demanding conditions: prolonged conversations drift, boundaries wobble, and affective continuity fails if retention is shallow or protections are unreliable.
Authenticity hinges upon four factors: latency below two seconds to preserve turn-taking fluid; identity cards with stable backstories and boundaries; audio models that carry timbre, rhythm, and breathing cues; and recall policies that keep important details without storing everything you say. To achieve safer fun, directly set guidelines in the first communications, don’t sharing identifying information, and choose providers that support on-device or end-to-end encrypted voice where available. When a conversation tool markets itself as a fully « uncensored virtual partner » but can’t show how it safeguards your chat history or maintains consent norms, step on.
Judging « realistic NSFW » image performance
Quality in some realistic adult generator is not so much about promotional claims and mainly about body structure, visual quality, and consistency across poses. The best AI-powered models handle skin fine detail, body part articulation, extremity and foot fidelity, and clothing-flesh transitions without boundary artifacts.
Undress pipelines tend to break on obstructions like folded arms, stacked clothing, straps, or locks—look for distorted jewelry, uneven tan marks, or shading that cannot reconcile with an original picture. Entirely synthetic creators fare superior in stylized scenarios but might still hallucinate extra fingers or misaligned eyes with extreme prompts. For realism assessments, compare generations across different poses and illumination setups, scale to two hundred percent for edge errors around the clavicle and waist area, and examine reflections in glass or glossy surfaces. When a platform hides source images after submission or prevents you from eliminating them, this is a deal-breaker regardless of image quality.
Protection and consent measures
Use only authorized, adult imagery and refrain from uploading identifiable photos of real people except when you have clear, written permission and a legitimate reason. Numerous jurisdictions pursue non-consensual synthetic nudes, and services ban automated undress application on actual subjects without consent.
Embrace a permission-based norm even in private settings: obtain clear authorization, store documentation, and preserve uploads anonymous when possible. Never attempt « clothing removal » on photos of people you know, well-known figures, or anyone under eighteen—age-uncertain images are off-limits. Avoid any platform that claims to circumvent safety protections or remove watermarks; those signals connect with regulation violations and increased breach risk. Finally, remember that purpose doesn’t erase harm: creating a illegal deepfake, even if one never share it, can yet violate regulations or policies of use and can be harmful to the person depicted.
Security checklist before using any undress app
Minimize risk via treating every undress app and online nude creator as a potential data sink. Favor providers that handle on-device or offer private options with full encryption and explicit deletion controls.
Prior to you upload: read the privacy policy for keeping windows and outside processors; verify there’s a delete-my-data process and a contact for deletion; avoid uploading identifying features or distinctive tattoos; remove EXIF from photos locally; use a burner email and billing method; and sandbox the application on some separate user profile. When the tool requests camera roll rights, refuse it and just share specific files. When you see language like « could use submitted uploads to improve our algorithms, » expect your submissions could be kept and train elsewhere or not at whatsoever. When in question, never not submit any image you wouldn’t be accepting of seeing leaked.
Spotting deepnude results and online nude tools
Recognition is incomplete, but forensic tells include inconsistent lighting, unnatural skin changes where clothing was, hair boundaries that clip into flesh, accessories that blends into any body, and reflected images that don’t match. Magnify in around straps, belts, and hand extremities—such « clothing stripping tool » often struggles with edge conditions.
Look for unnaturally uniform pores, repeating texture tiling, or blurring that attempts to hide the transition between artificial and original regions. Check metadata for absent or standard EXIF when the original would include device tags, and run reverse photo search to check whether the face was lifted from another photo. Where available, verify C2PA/Content Authentication; various platforms embed provenance so users can determine what was edited and by who. Employ third-party detectors judiciously—these systems yield false positives and errors—but merge them with visual review and authenticity signals for better conclusions.
What should one do if a person’s image is used non‑consensually?
Respond quickly: maintain evidence, submit reports, and utilize official takedown channels in parallel. You don’t require to establish who created the fake content to begin removal.
First, capture URLs, timestamps, screen screenshots, and hashes of the pictures; preserve page source or stored snapshots. Second, flag the images through the website’s impersonation, adult material, or fake content policy forms; numerous major services now provide specific unauthorized intimate image (NCII) mechanisms. Third, file a deletion request to search engines to limit discovery, and file a DMCA takedown if someone own the original photo that was manipulated. Fourth, contact local police enforcement or a cybercrime department and give your proof log; in various regions, NCII and deepfake laws allow criminal or judicial remedies. If you’re at risk of continued targeting, think about a alert service and talk with a digital safety nonprofit or lawyer aid group experienced in non-consensual content cases.
Obscure facts worth knowing
Point 1: Many services fingerprint images with perceptual hashing, which enables them find exact and close uploads across the internet even following crops or slight edits. Fact 2: The Digital Authenticity Organization’s C2PA system enables digitally signed « Content Credentials, » and a growing amount of devices, editors, and online platforms are implementing it for provenance. Fact 3: Both Apple’s App Store and Android Play restrict apps that support non-consensual adult or sexual exploitation, which represents why many undress applications operate solely on a web and outside mainstream marketplaces. Point 4: Cloud companies and core model providers commonly ban using their systems to produce or publish non-consensual explicit imagery; if some site claims « uncensored, no limitations, » it might be breaching upstream policies and at higher risk of sudden shutdown. Point 5: Malware hidden as « clothing removal » or « AI undress » programs is common; if a tool isn’t internet-based with transparent policies, treat downloadable files as hostile by assumption.
Closing take
Use the appropriate category for each right purpose: relationship chat for roleplay experiences, adult image generators for generated NSFW imagery, and refuse undress applications unless you possess explicit, mature consent and some controlled, private workflow. « Free » usually includes limited access, watermarks, or inferior quality; subscriptions fund the GPU time that allows realistic chat and visuals possible. Above all, regard privacy and permission as mandatory: restrict uploads, secure down deletions, and walk away from every app that implies at harmful misuse. If one is evaluating providers like N8ked, DrawNudes, different apps, AINudez, several tools, or similar platforms, experiment only with de-identified inputs, verify retention and erasure before you engage, and never use photos of actual people without clear permission. High-quality AI services are attainable in the current era, but they’re only beneficial it if users can achieve them without breaching ethical or lawful lines.
